Using Okta as an External IDP with SAML¶
Follow the instructions below to connect Okta as a third party Identity Provider to WSO2 API Manager.
Prerequisites¶
Before you begin, make sure you do the following.
- Create an account in https://developer.okta.com/
- Download WSO2 API Manager distribution from https://wso2.com/api-management/
- Unzip the distribution and open the
deployment.tomlfile located in<APIM_HOME>/repository/conf/. Add the following configurationYou need to enable this because Okta uses the email as the username by default. To use the email as the username in WSO2 API Manager you have to enable it as it is not enabled by default. Once enabled, you can use your email or a normal username as your username.[tenant_mgt] enable_email_domain= true - Start the WSO2 API Manager server.
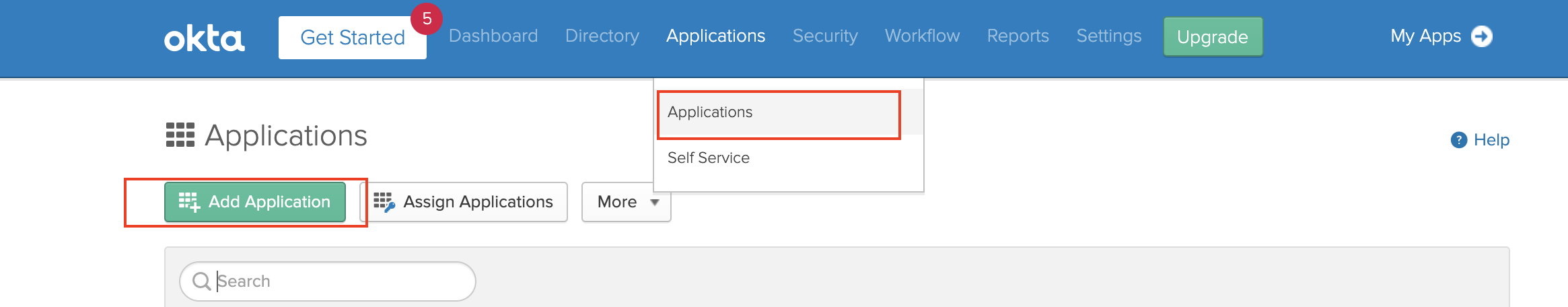
Step 1 - Configure Okta¶
-
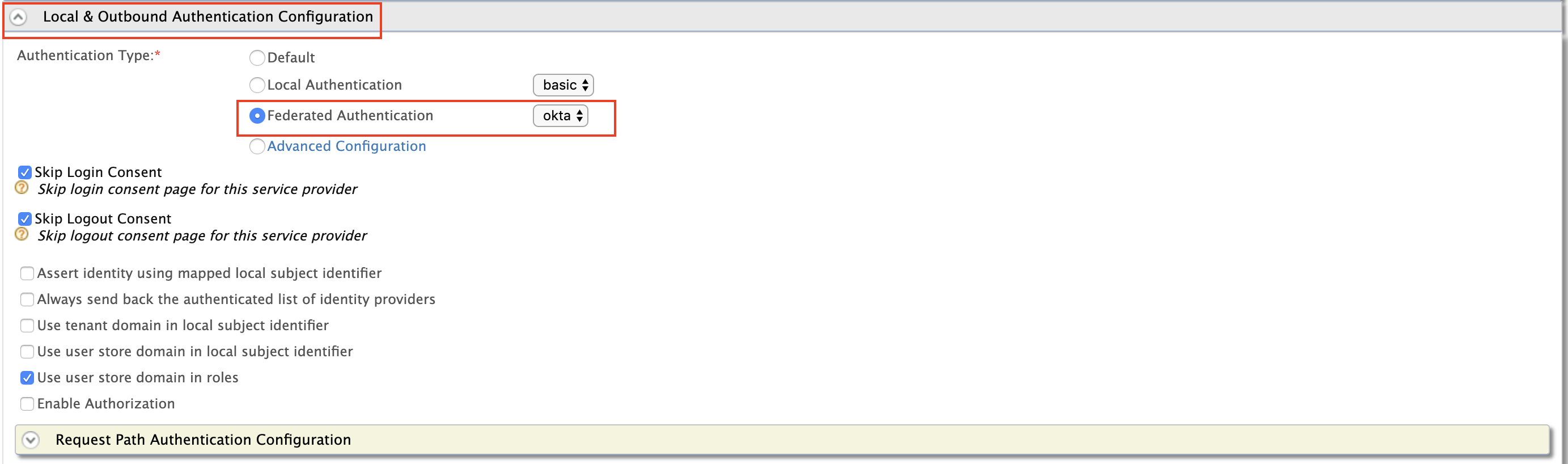
Login to the Okta developer console and switch to the classic UI.
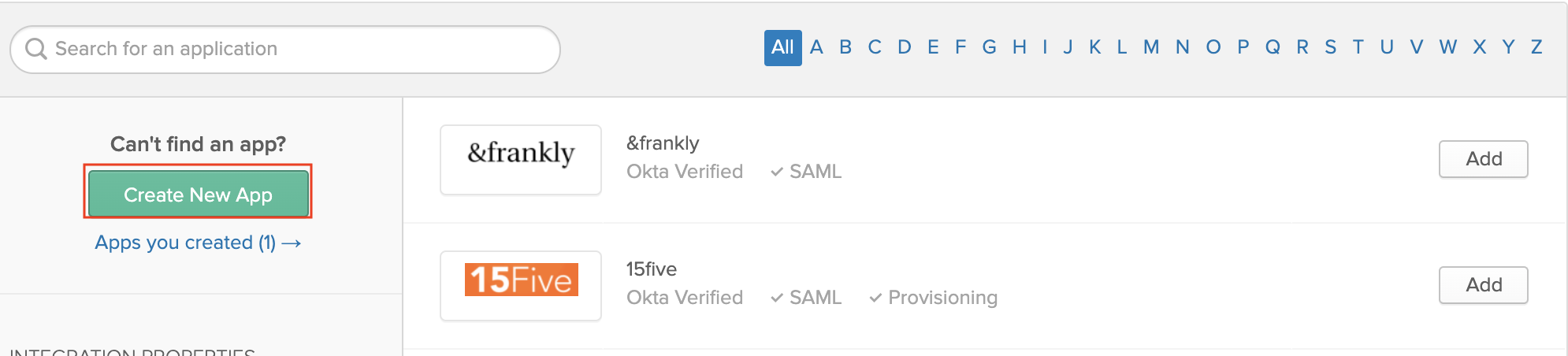
-
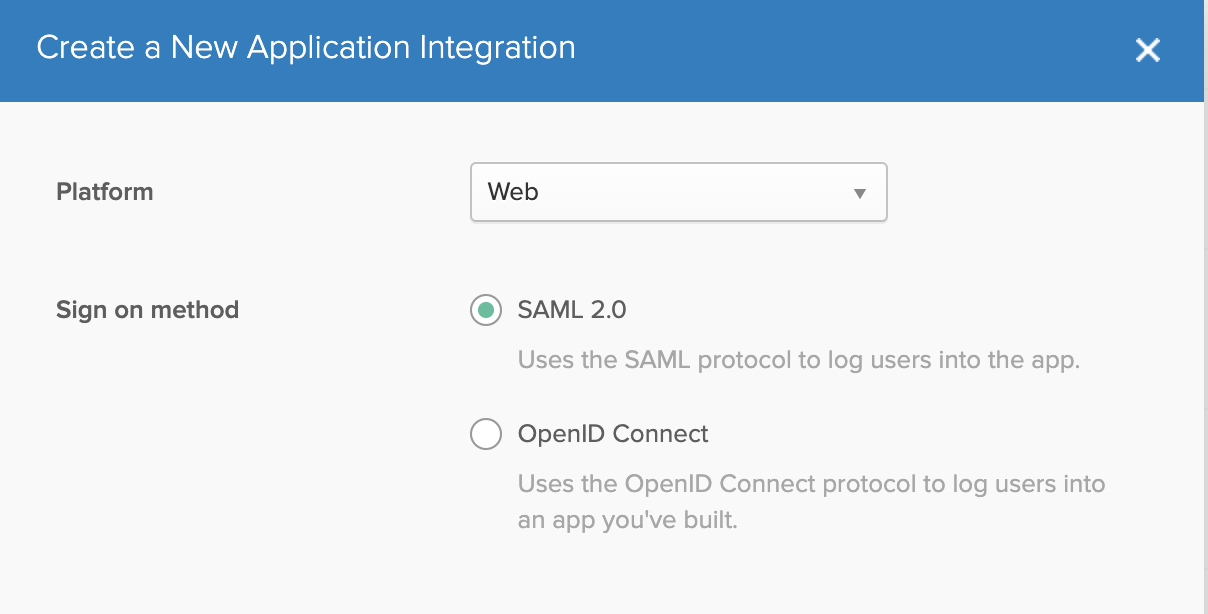
Select Web as the Platform. Select SAML 2.0 as the sign-on method.
-
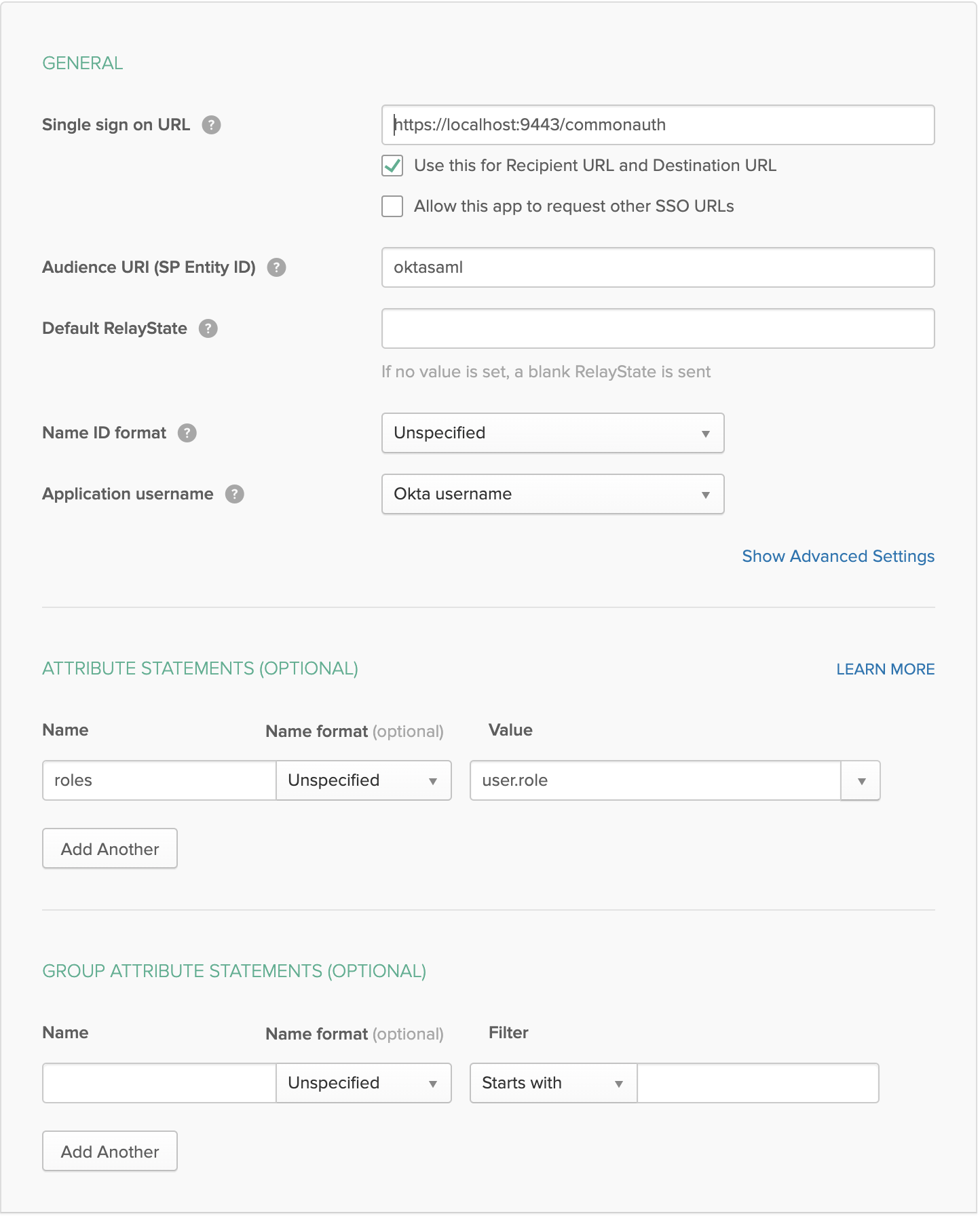
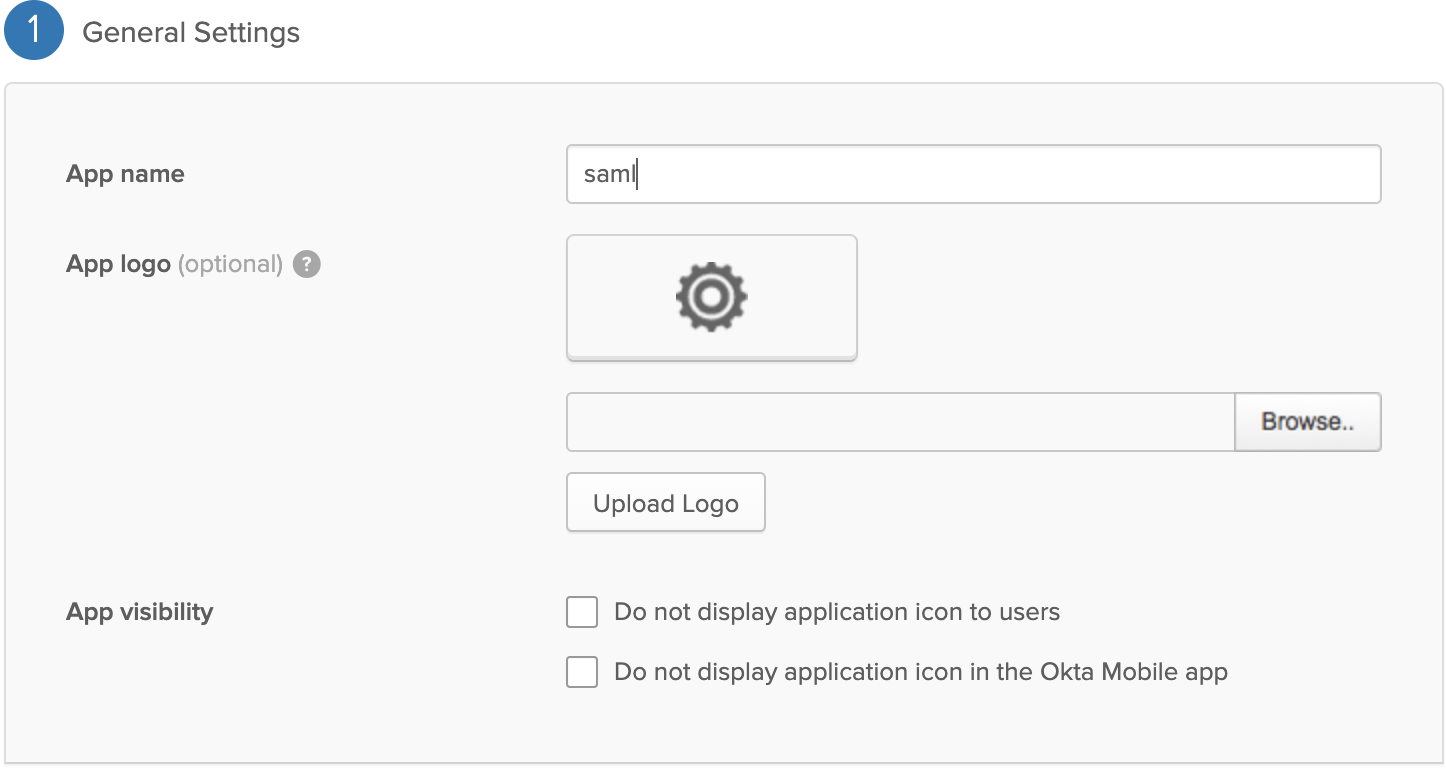
Enter the General Settings as shown in the images below.
Warning
Audience URI should be same as the Identity Provider entity id name that is created in WSO2 API Manager.
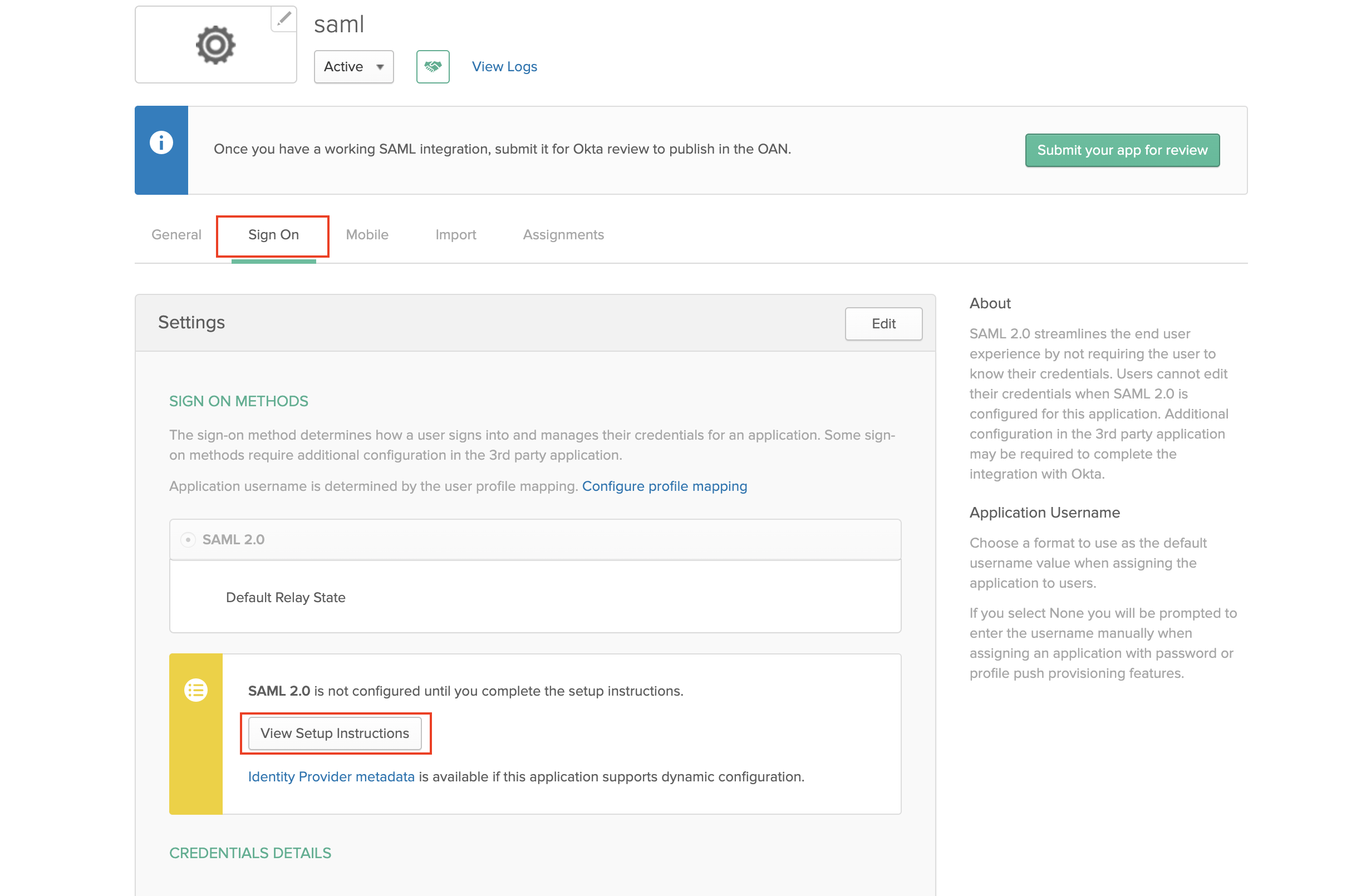
-
Inside the SAML app you created go to Sign On and click View Setup Instructions.
-
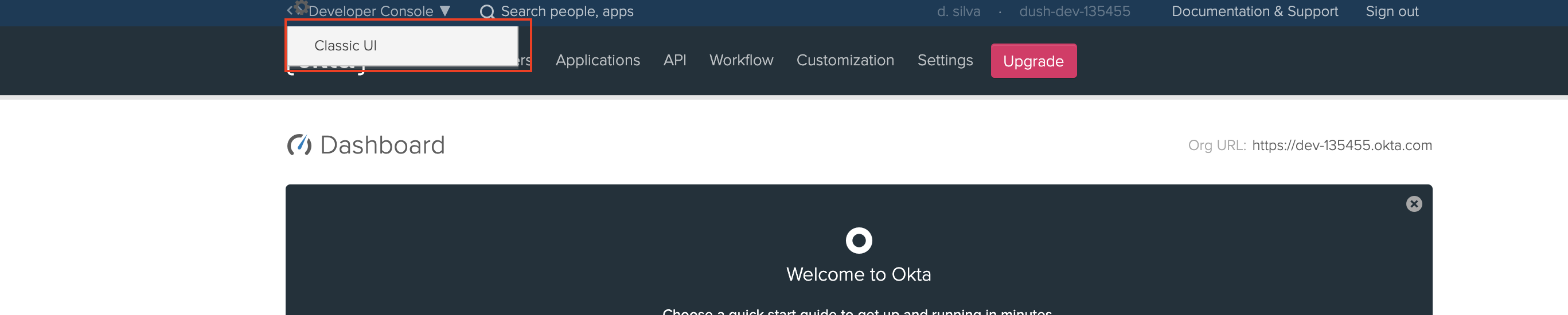
Switch back to the Developer Console shown in step 1.
-
Follow these steps to add a new attribute to the default user profile of Okta to represent the user role.
-
Enter the user attributes shown in the image below. Click Save.
-
Follow the steps below to edit the user profile.
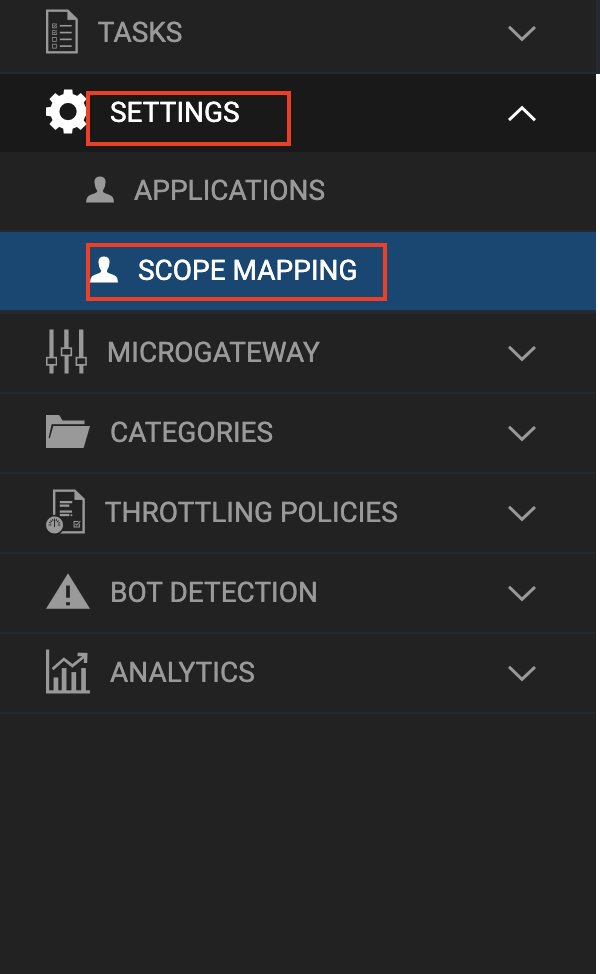
Step 2 - Setup API-Manager¶
-
Log in to
https://localhost:9443/carbon. -
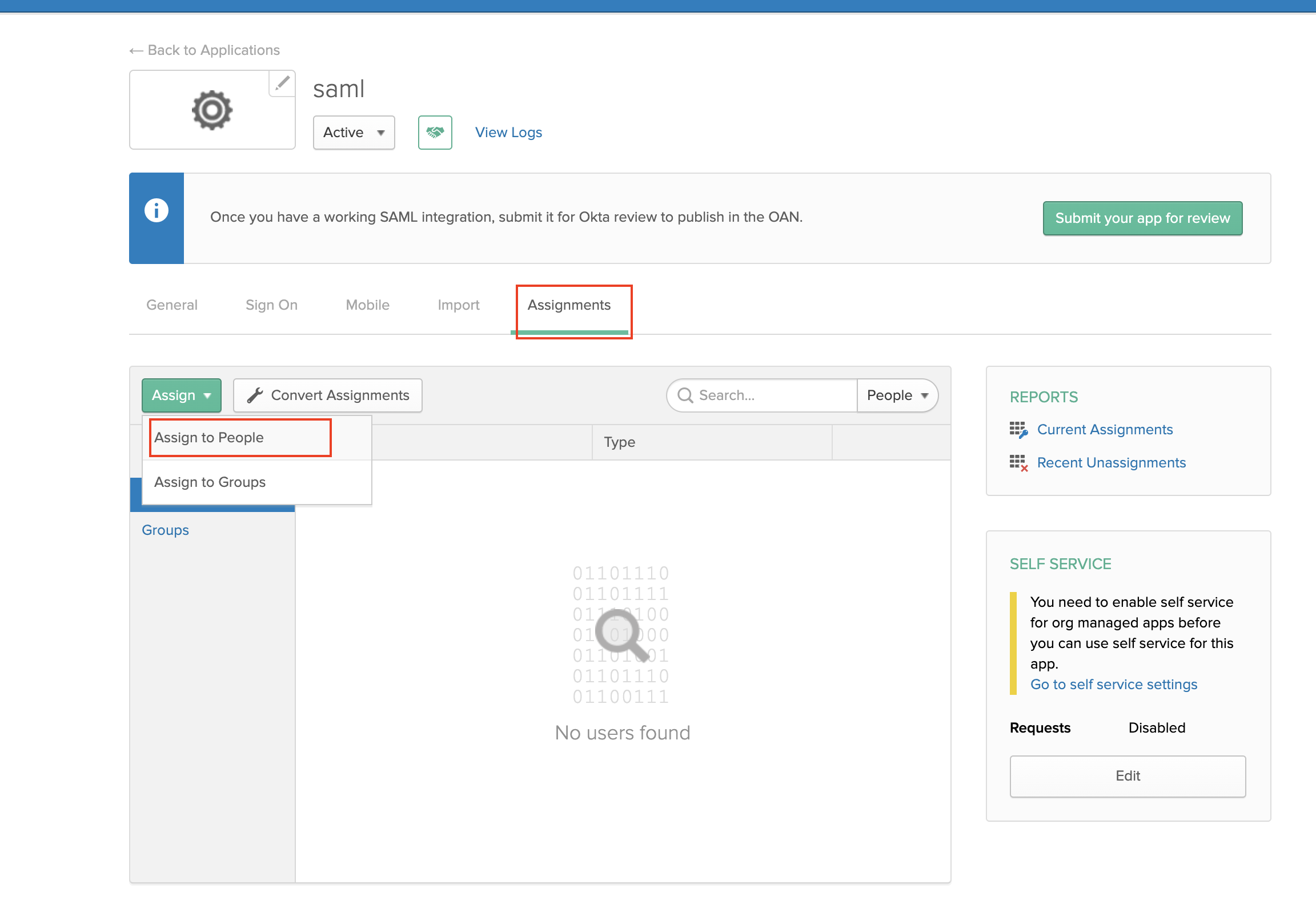
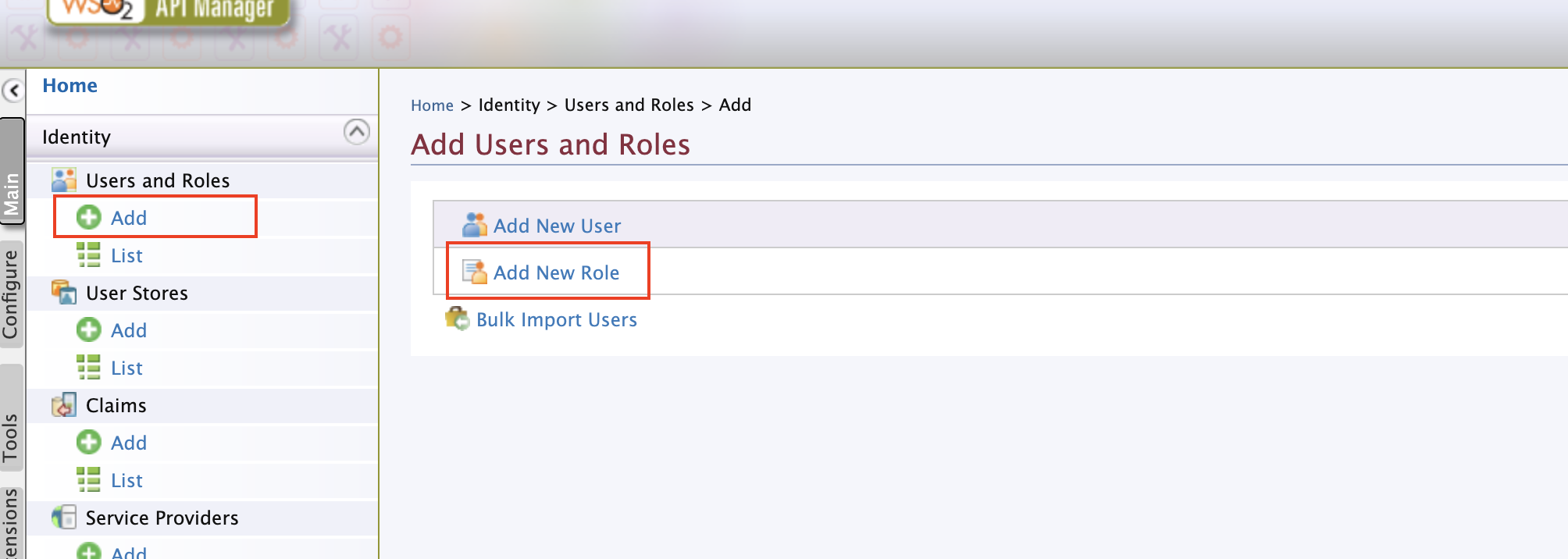
Create a role that needs to be assigned to users that will be provisioned from Okta.
-
Log in to
https://localhost:9443/admin. -
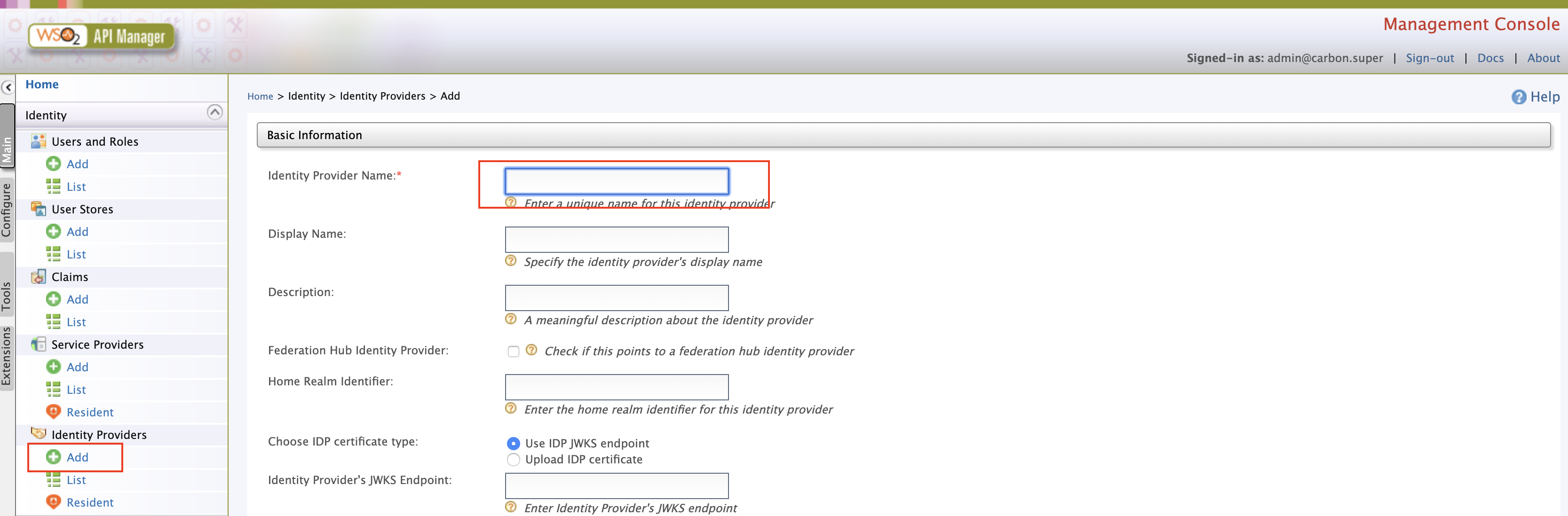
Add an Identity Provider.
-
Sign in to the WSO2 API-M Management Console.
https://localhost:9443/carbon -
Click Main and then click Add under Identity Providers.
-
Enter the Identity Provider's Name.
-
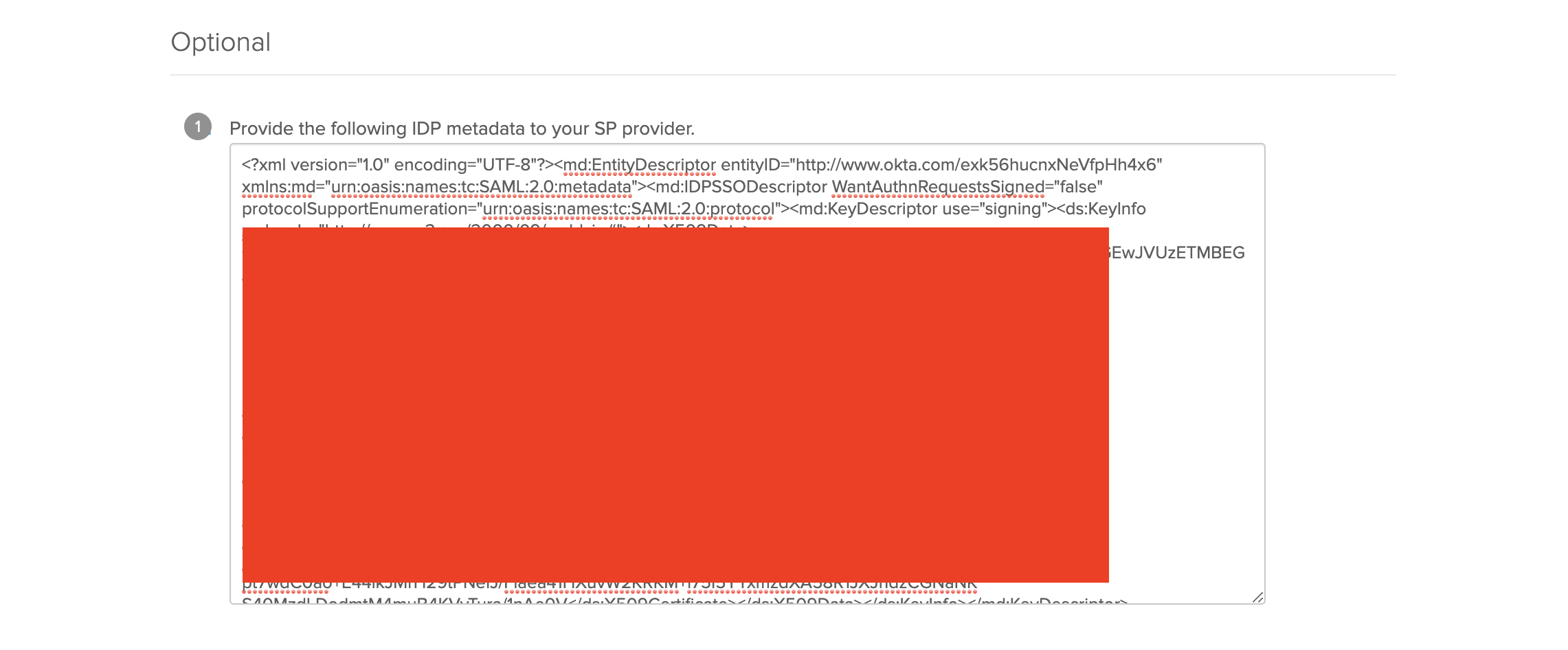
Expand Federated authenticators -> SAML2 Web SSO Configuration section. Under Select Mode, select Metadata File Configuration. Update the XML file obtained during the Okta setup process Step 1 - 6(a).
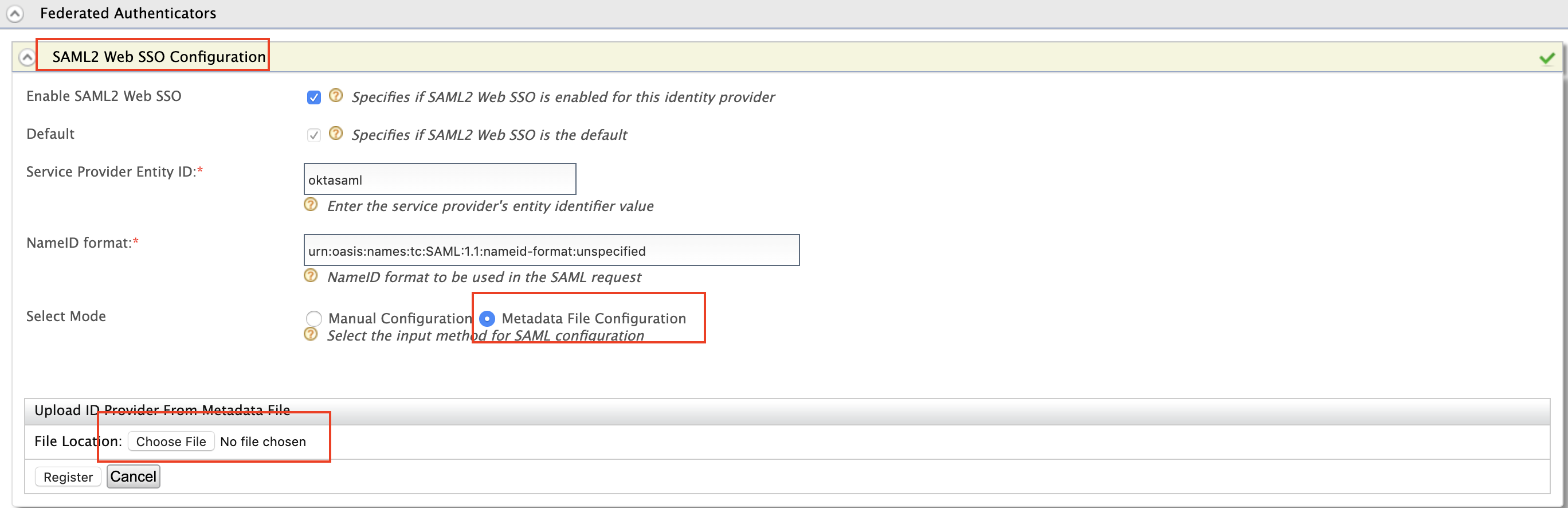
Field Sample value Specifies if SAML2 Web SSO is enabled for this Identity Provider True Service Provider Entity ID Entity ID specified when creating SAML app (e.g., oktasaml) -
-
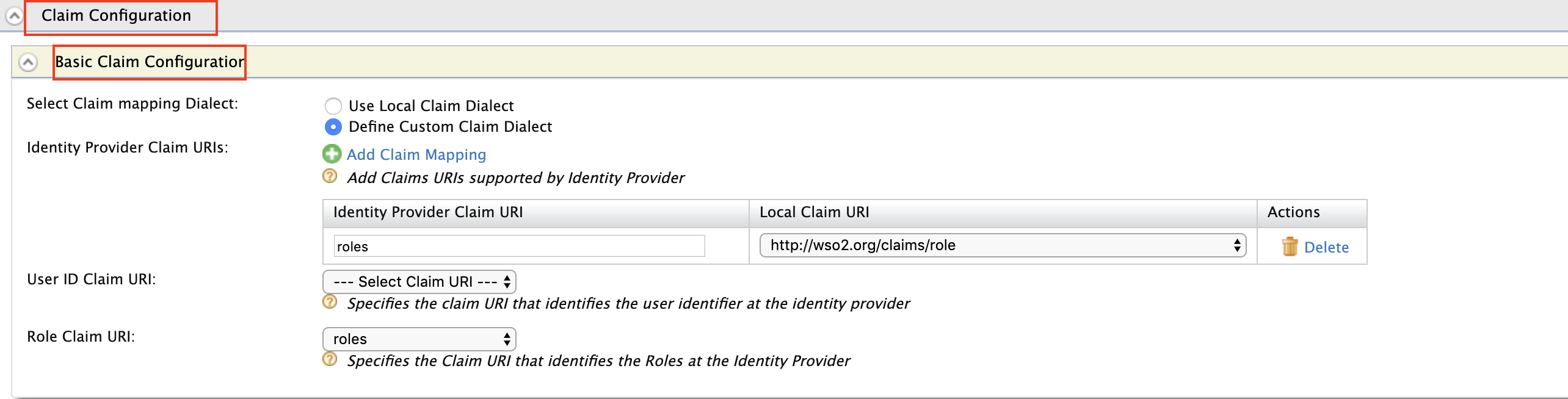
Expand Claim Configuration -> Basic Claim Configuration. Add the claim configurations as shown in the image below. The
roledrop-down menu contains the roles you configured in Okta (Step 1). Select theIdentity Provider Claim URIsaccording to the configurations in the Okta Developer Console in Step 1. -
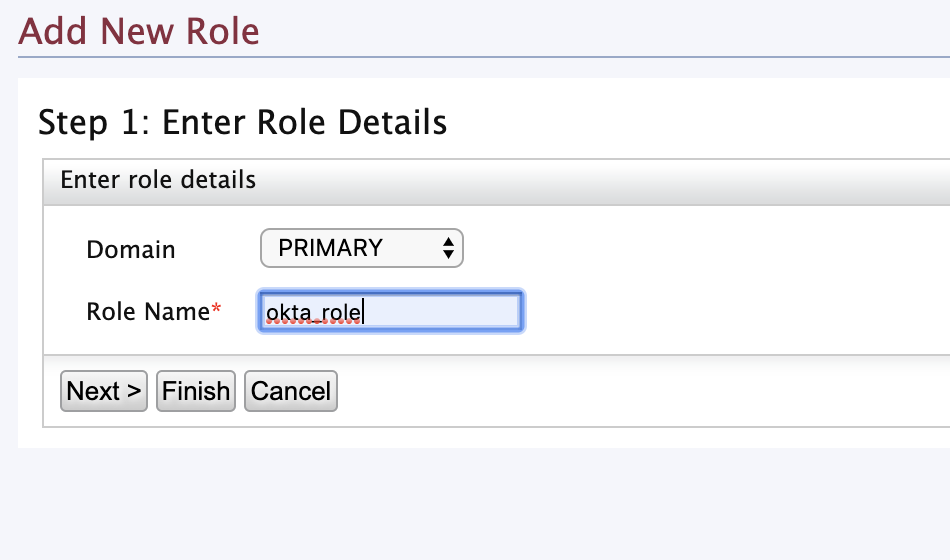
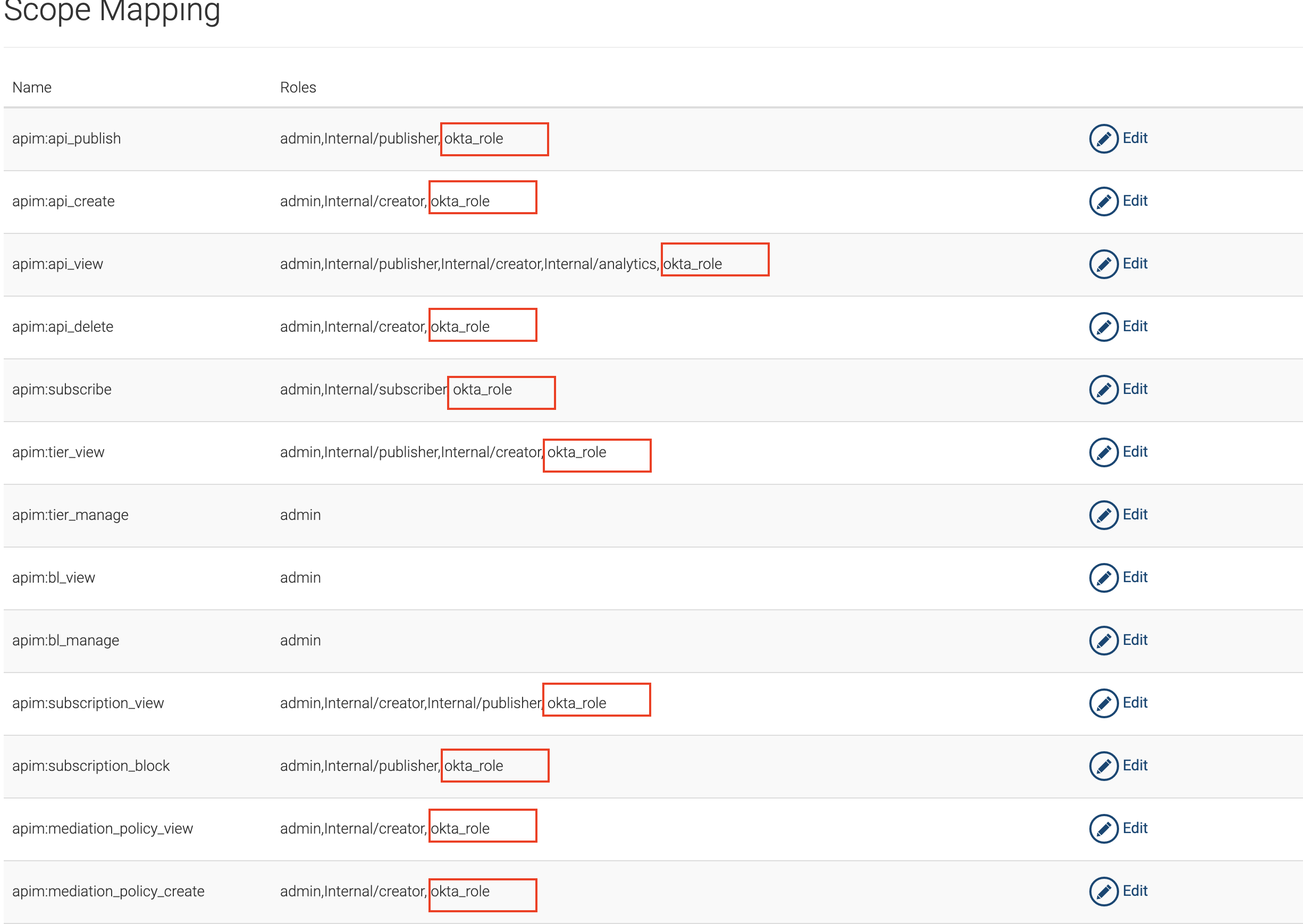
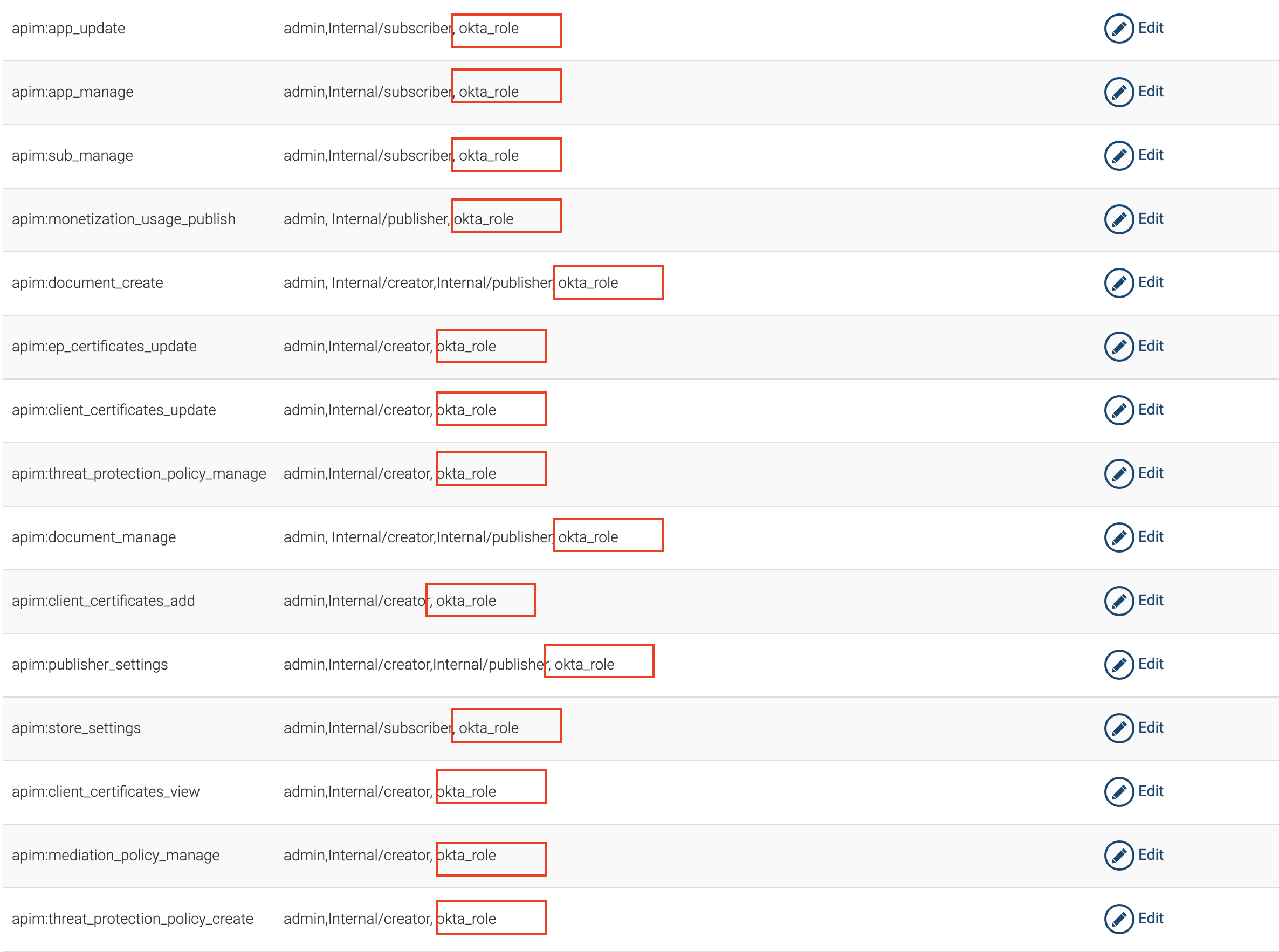
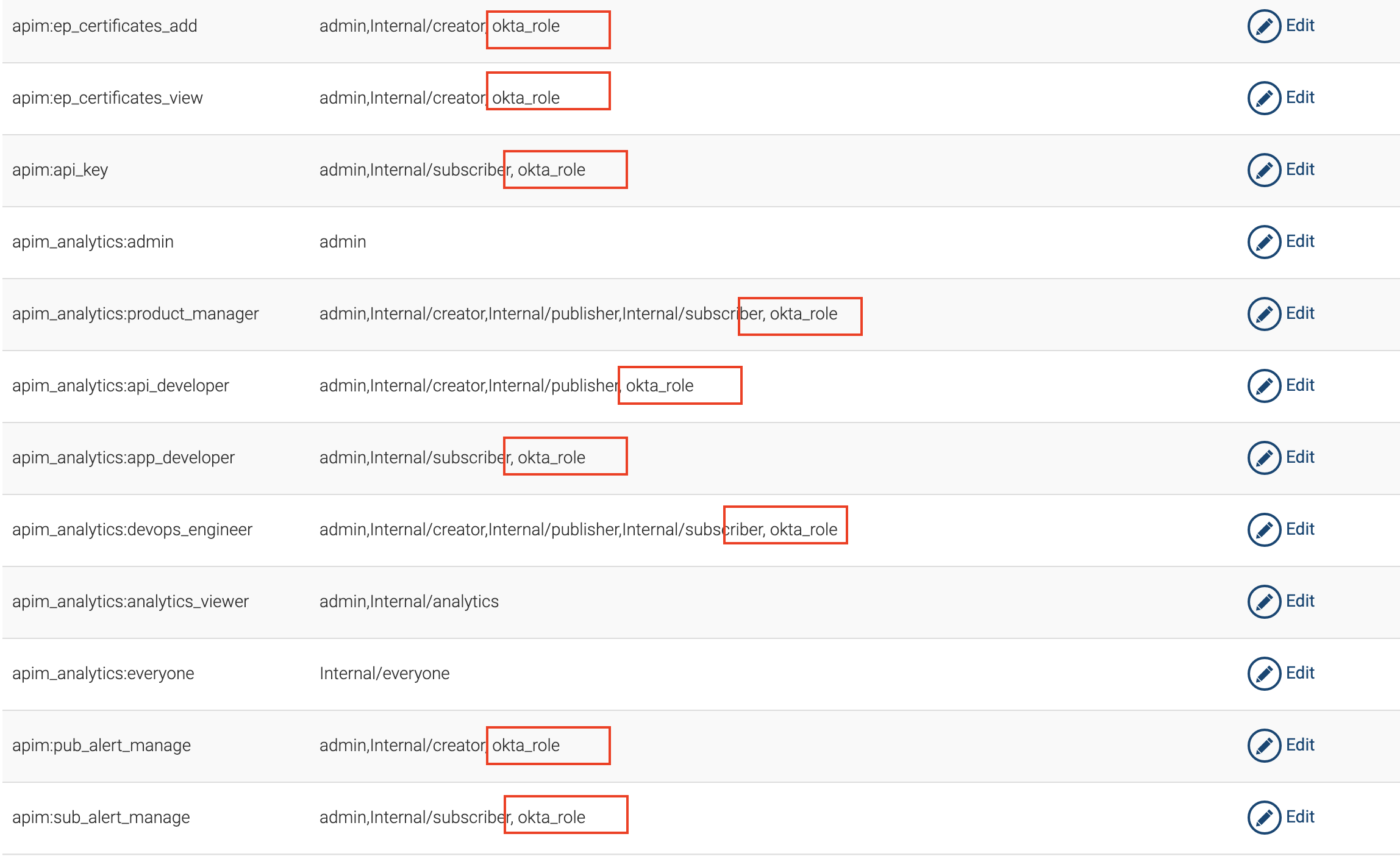
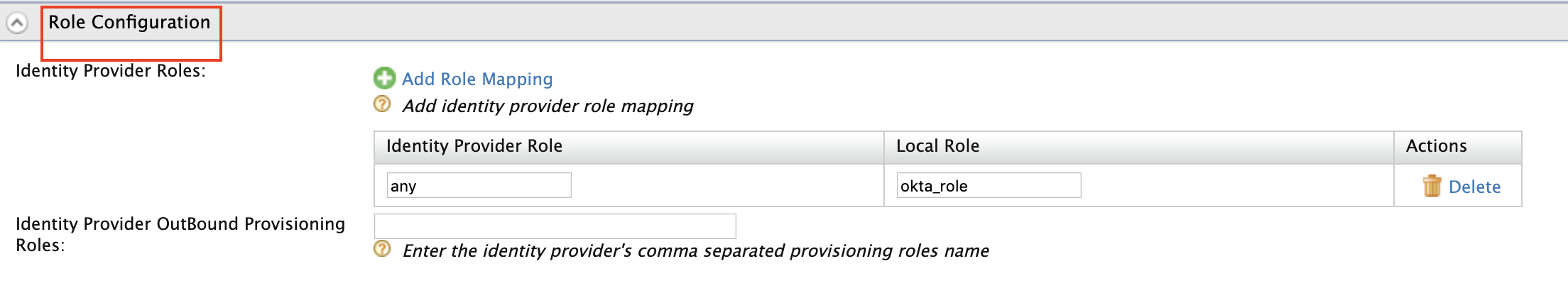
Expand Role configuration and add
okta_roleas shown below.You can check if the user logged in has the role
anyand assign the localokta_role. -
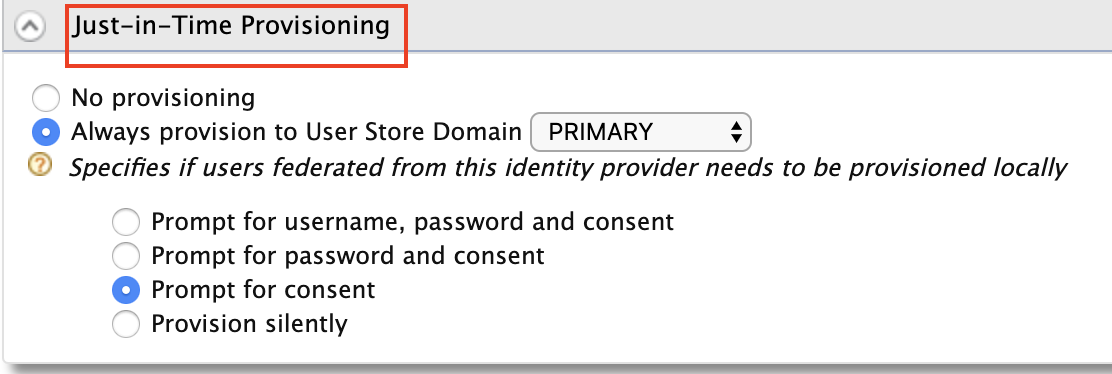
Enable Just-in-Time Provisioning for the user to be saved in the API Manager user store.
-
Select a Service Provider.
-
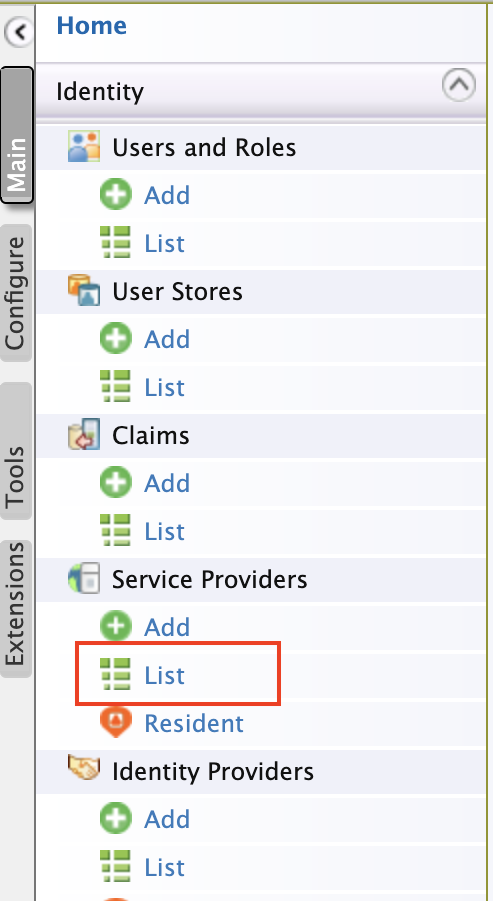
Navigate to Service Providers -> List.
-
There are two service providers created
apim_publisherandapim_devportal. Click Edit forapim_publisher.Warning
You need to have signed in to the Developer Portal and Publisher at least once for the two service providers to appear, as it is created during the first sign in.
-
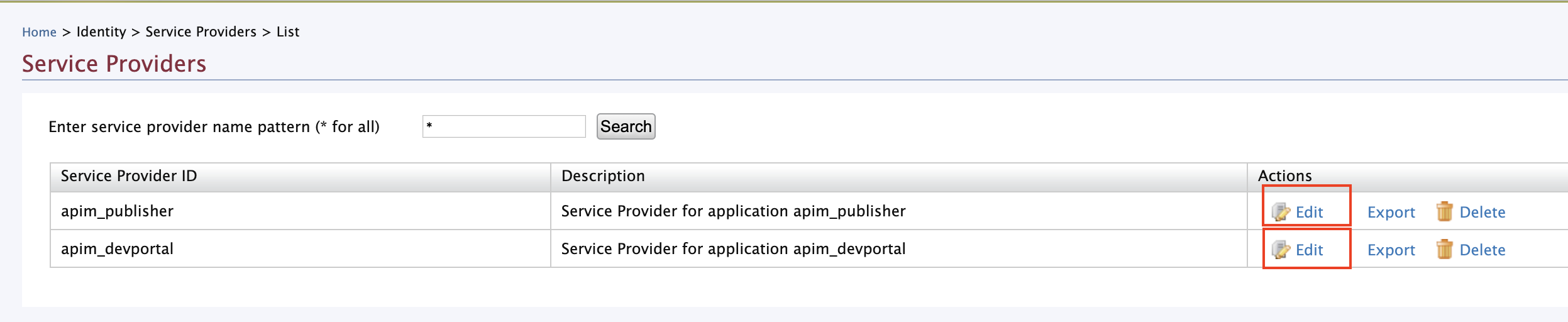
Expand Local & Outbound Authentication Configuration. Select Federated Authentication and select the name of the Identity Provider you created from the corresponding drop-down menu.
Repeat this step for
apim_devportalas a Service Provider. -
Now you will be able to Sign in to the Publisher and Developer Portal using Okta.