Identity Management for the API Developer Portal¶
Identity management for the API developer portal includes the following features.
Password Recovery¶
Password recovery feature does not work by default because an email server is not configured to send the password recovery email. Follow the steps below to enable password recovery feature for the API Developer Portal.
-
Open the
<API-M_HOME>/repository/conf/deployment.tomlfile and add a mail server configuration as shown below. See Configuring the Email Sending Module for more information.[output_adapter.email] from_address = "[email protected]" username = "wso2amtest" password = "Wso2@am70" hostname = "smtp.gmail.com" port = "587" enable_start_tls = true enable_authentication = true -
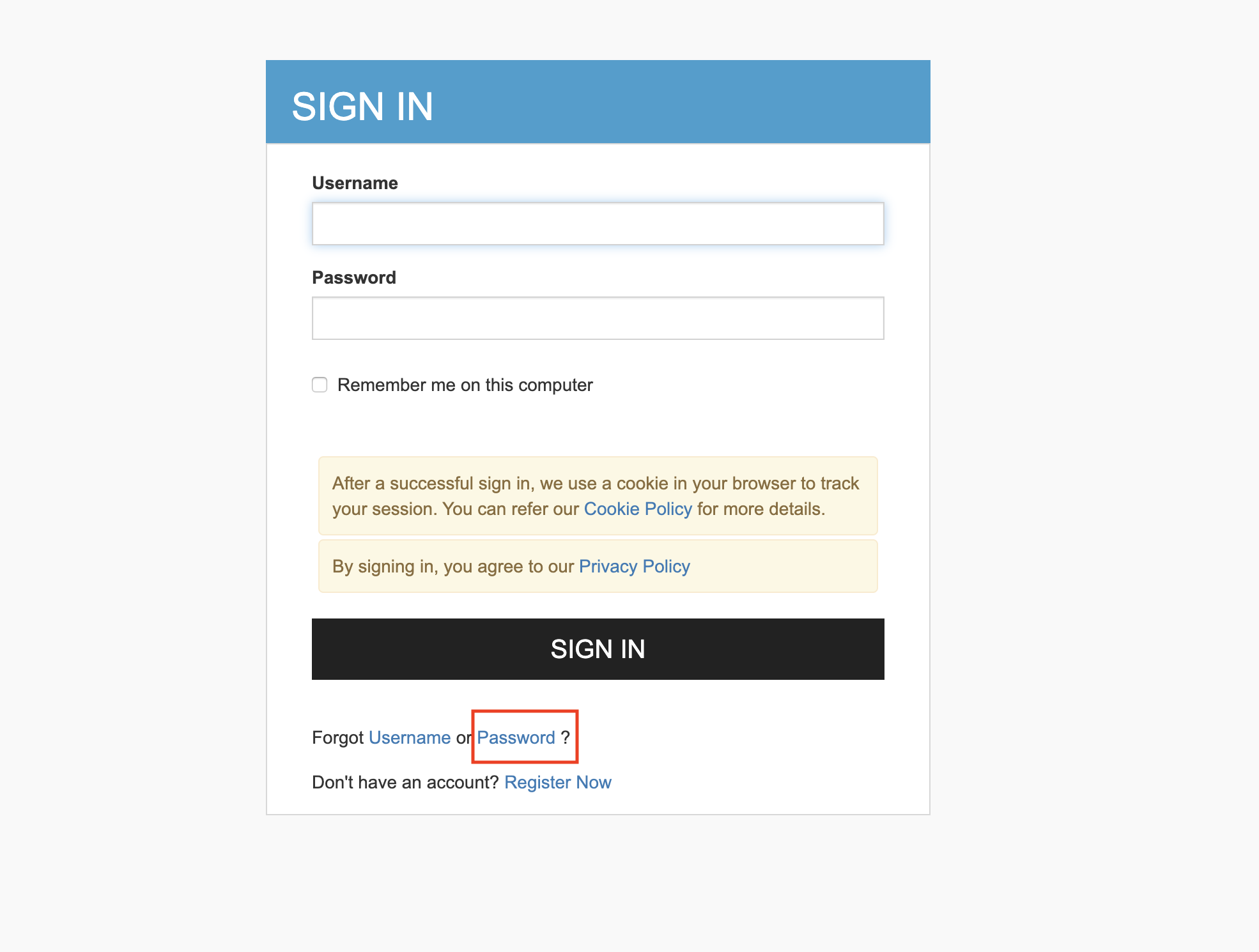
After the mail server is configured, the user can click on the Forgot Password link on the Sign In page of the API Developer Portal and request a password change.
-
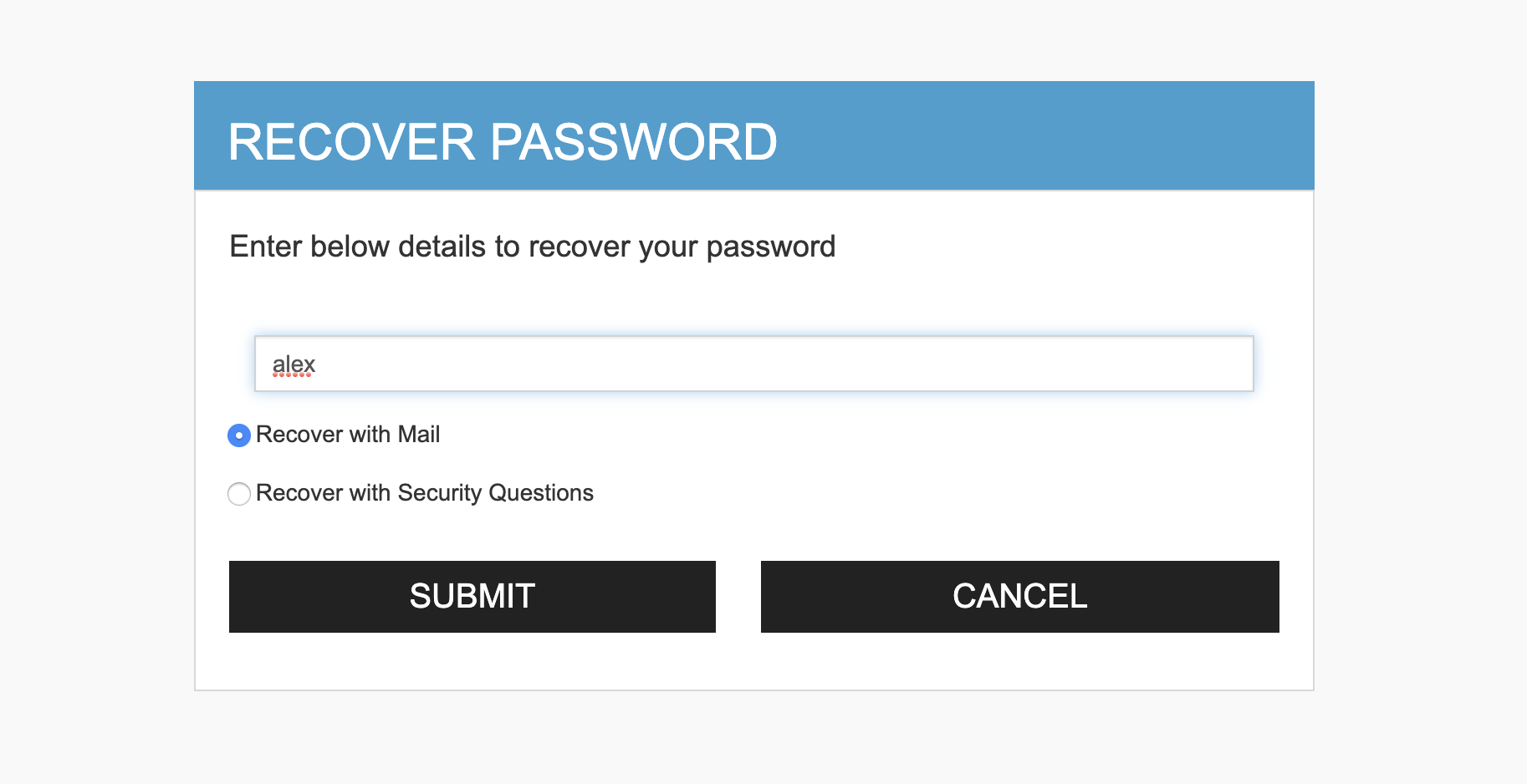
Enter the username you are trying to recover the password of and click Submit.
-
You will receive an email with instructions to reset your password. Note that this is email is sent to the email address stored during user sign up.
Note
You can change the the template of this email (E.g., email link, message body, etc.). To edit the mail template, open the
<API-M_HOME>/repository/conf/email/email-admin-config.xmlfile and make the changes.
Account locking¶
You can lock user accounts with the Account recovery and credential management feature, pre-installed in WSO2 API Manager.
Account locking by failed login attempts¶
The following steps show how to enable account locking. See Account Locking by Failed Login Attempts for more information.
-
Log into the Management Console(
https://<API-M_HOST>:<API-M_PORT>/carbon) using admin credentials.. -
Click Resident under Identity Providers found in the Main tab.
-
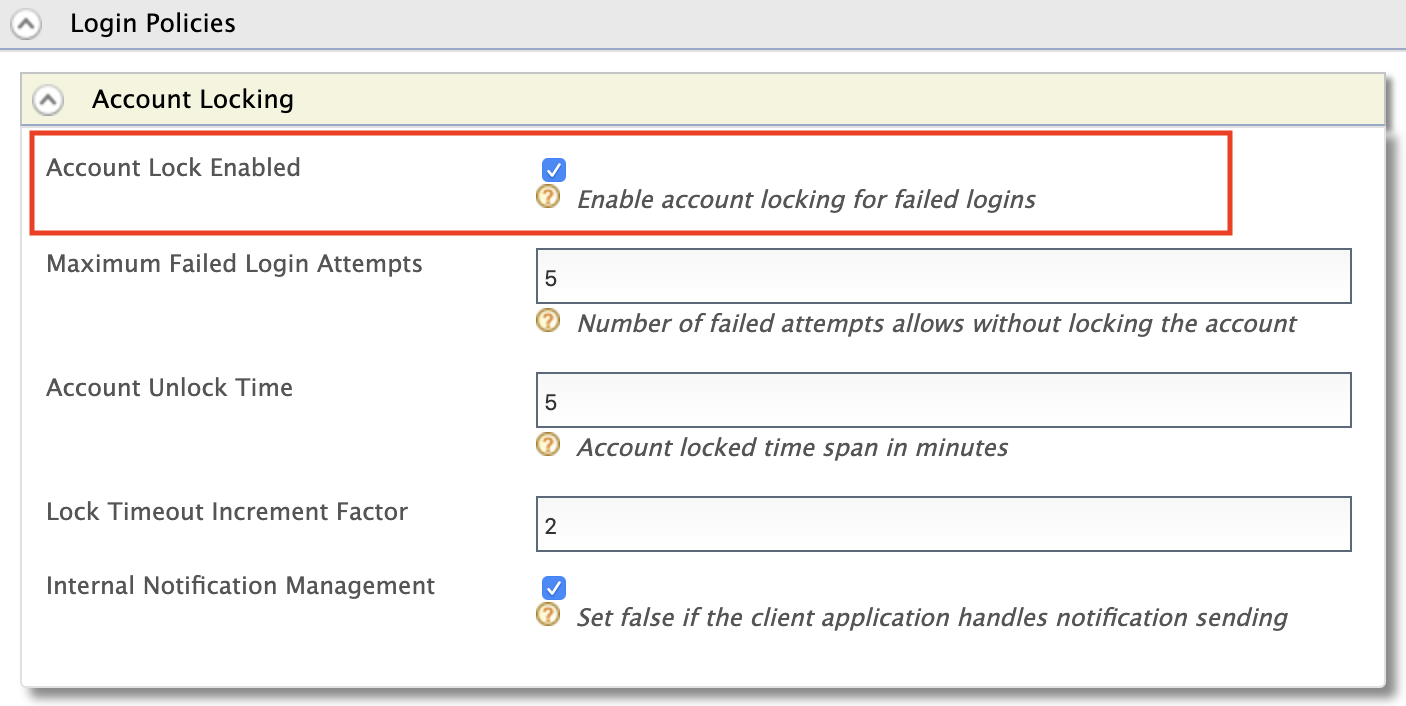
Expand the Login Policies tab.
-
Expand the Account Locking tab and tick the Account Lock Enabled checkbox. Click Update to save changes.
Info
An error message similar to the following will be logged in wso2carbon.log when the account is locked.
ERROR - Account is locked for user alex in user store PRIMARY in tenant carbon.super. Cannot login until the account is unlocked.Account locking by an administrative user¶
An administrative user can lock and unlock a particular user's account through the management console. See Locking a Specific User Account for more information.
-
Log in to the Management Console(
https://<API-M_HOST>:<API-M_PORT>/carbon) using admin credentials. -
Go to Claims > List on the Main tab and select the
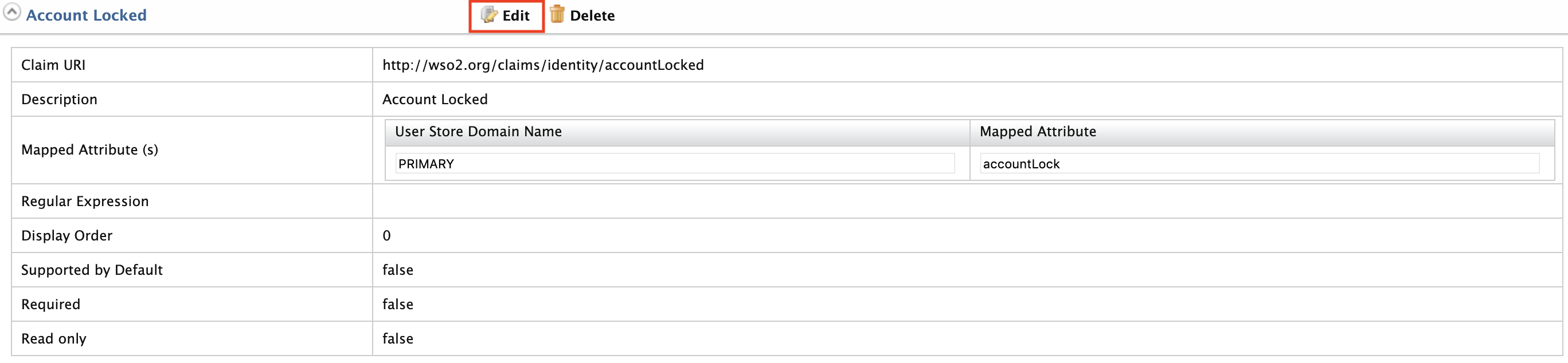
http://wso2.org/claimsclaim dialect. -
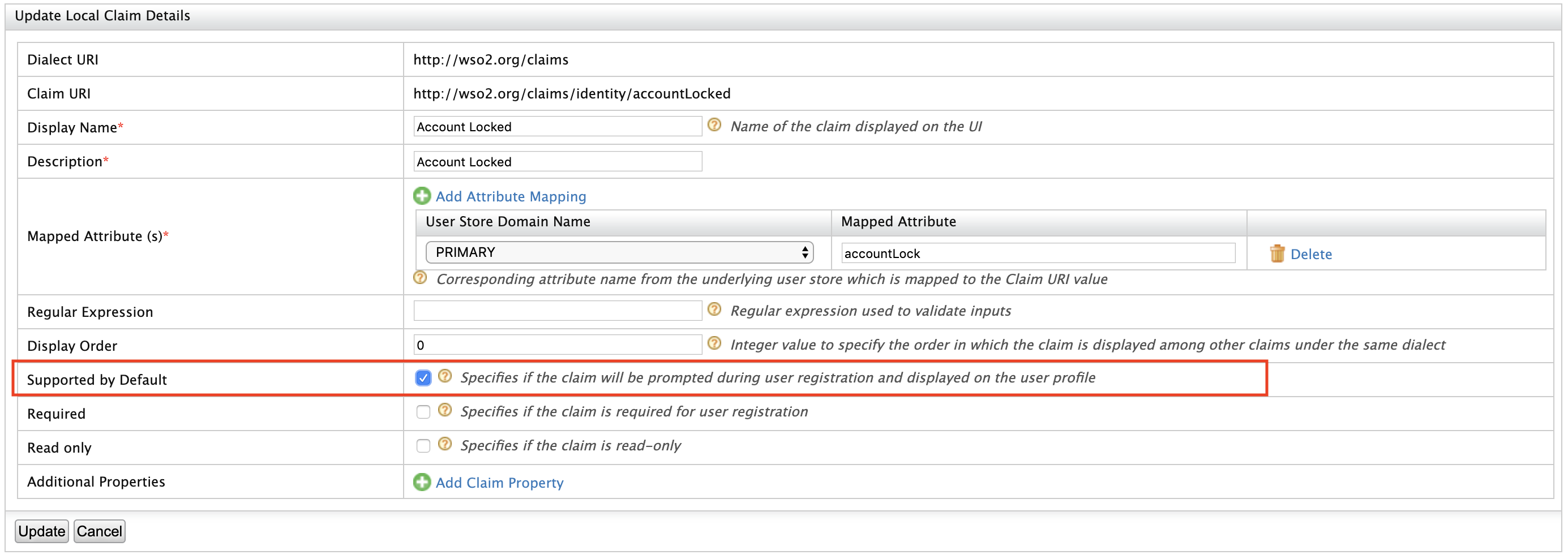
Expand the Account Locked claim and click Edit .
-
Tick the Supported by Default checkbox and click Update. This is done to make the Account Locked status appear in the user's profile.
-
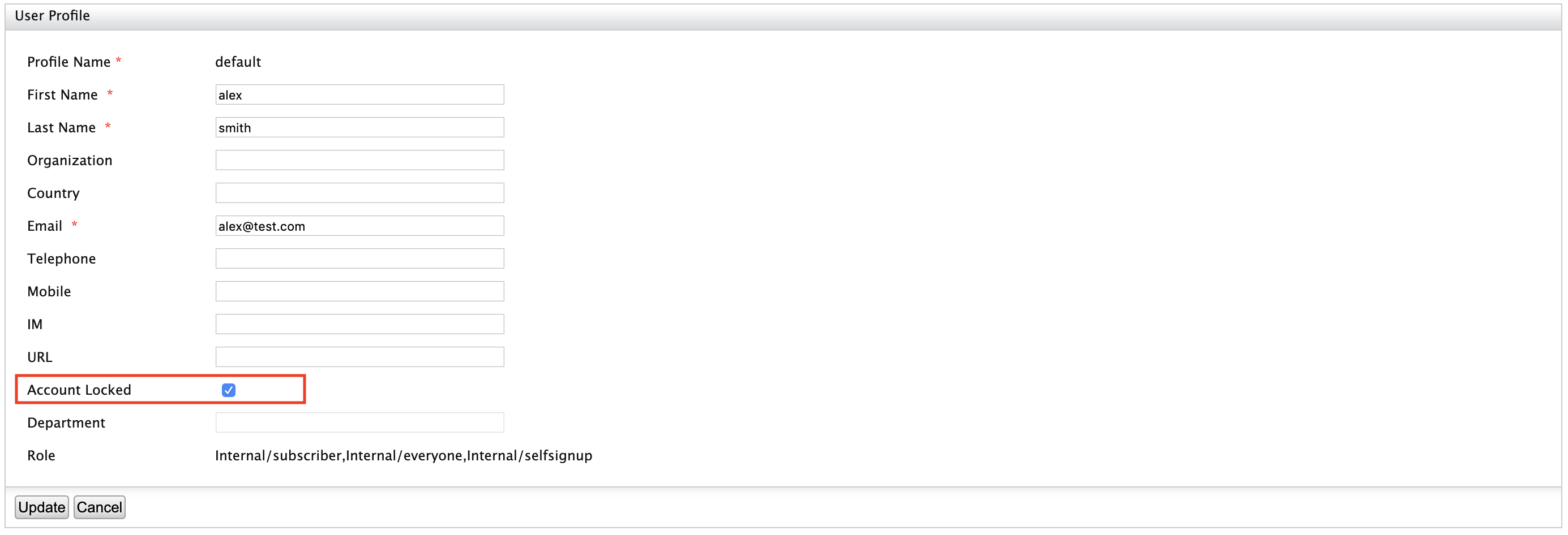
Go to Users and Roles > List > Users on the Main menu and click on User Profile of the user you want to lock.
-
Tick the checkbox in front of the Account Locked field to lock the account for the user and click Update .
Password policies¶
You can define custom password policies for API developer portal user signup. Open the <API-M_HOME>/repository/conf/deployment.toml file and add the password policy configuration based on your preference as shown below. See Writing a Custom Password Validator for more information.
[identity_mgt.events.schemes]
passwordPolicy.properties.enable = true
passwordPolicy.properties.'min.length' = 4
passwordPolicy.properties.'max.length' = 10
passwordPolicy.properties.pattern = "^((?=.*\\\\d)(?=.*[a-z])(?=.*[A-Z])(?=.*[!@#$%&*])).{0,100}$"
passwordPolicy.properties.errorMsg = "Password pattern policy violated. Password should contain a digit[0-9], a lower case letter[a-z], an upper case letter[A-Z], one of !@#$%&* characters"
passwordPolicy.properties.'class.PasswordLengthPolicy' = "org.wso2.carbon.identity.mgt.policy.password.DefaultPasswordLengthPolicy"
passwordPolicy.properties.'class.PasswordNamePolicy' = "org.wso2.carbon.identity.mgt.policy.password.DefaultPasswordNamePolicy"
passwordPolicy.properties.'class.PasswordPatternPolicy' = "org.wso2.carbon.identity.mgt.policy.password.DefaultPasswordPatternPolicy"