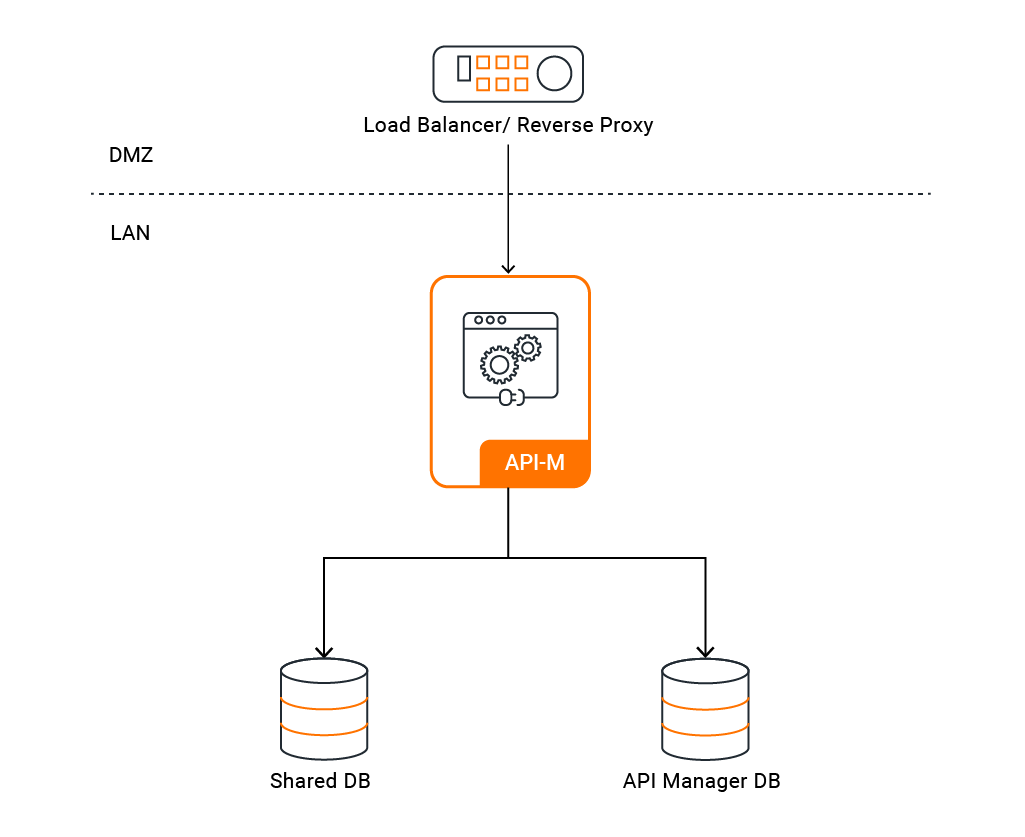
Pattern 0: API-M Deployment with All-in-One Setup¶
This deployment consists of a single API-M node with a single API-M runtime. You can use this pattern if you expect to receive low traffic to your deployment and do not need any high availability in your environment.
Info
For advanced details on the deployment pattern, please refer to the official documentation.
Contents¶
- Pattern 0: API-M Deployment with All-in-One Setup
- Contents
- Prerequisites
- Step 1 - Set Up Basic Configurations
- Minimal Configuration
- Configuration
Prerequisites¶
Before you begin, ensure you have the following prerequisites in place:
Step 1 - Set Up Basic Configurations¶
Info
The following tools and configurations are necessary for deploying WSO2 API-M in a Kubernetes environment.
- Install the required tools:
- Git
- Helm
-
Ensure you have a running Kubernetes cluster.
-
Install a routing controller. Choose either:
- Envoy Gateway (enabled by default) - RECOMMENDED (modern Gateway API-based routing)
- NGINX Ingress Controller (disabled by default) - DEPRECATED (traditional Ingress-based routing)
-
Add the WSO2 Helm chart repository:
helm repo add wso2 https://helm.wso2.com && helm repo update
Minimal Configuration¶
If you want to quickly try out WSO2 API Manager on Kubernetes with minimal configuration, you can use the default values provided in the default_values.yaml file.
Quick Start Configuration
This minimal configuration includes:
- H2 database (embedded)
- Default keystore and truststore
- Basic settings for testing purposes
Note: This configuration is ideal for development environments or quick evaluation but is not recommended for production use.
Before running the Helm install command, set wso2.apim.configurations.encryption.key in the default values file.
- Create a namespace for the deployment
kubectl create namespace apim
- Install the Envoy Gateway as follows:
helm install envoy-gateway oci://docker.io/envoyproxy/gateway-helm \
--version v1.7.0 -n envoy-gateway-system \
--set config.envoyGateway.extensionApis.enableBackend=true \
--set envoyGateway.gateway.experimentalFeatures.enabled=true \
--create-namespace
- Apply the sample Gateway manifest to create Gateway and GatewayClass resources.
kubectl apply -f https://raw.githubusercontent.com/wso2/helm-apim/4.7.x/docs/assets/sample-gateway.yaml -n apim
- Deploy API Manager with minimal configuration using the following command.
helm install apim wso2/wso2am-all-in-one --version 4.7.0-1 -f https://raw.githubusercontent.com/wso2/helm-apim/4.7.x/docs/am-pattern-0-all-in-one/default_values.yaml -n apim
The Helm chart uses Gateway API by default. If you prefer Ingress instead, follow the steps in 1.1 Add Gateway API controller or Ingress controller to configure and enable it.
Configuration¶
1. General Configuration of Helm Charts¶
The helm charts for the API Manager deployment are available in the WSO2 Helm Chart Repository. You can either use the charts from the repository or clone the repository and use the charts from the local copy.
Resource Naming Convention
The helm naming convention for APIM follows a simple pattern:
<RELEASE_NAME>-<CHART_NAME>-<RESOURCE_NAME>
1.1 Add Gateway API controller or Ingress controller
You can use either Envoy Gateway (Gateway API-based) or NGINX Ingress Controller (Ingress-based) for routing traffic to API Manager. By default, charts are configured to use Envoy Gateway. If you want to use NGINX Ingress Controller instead, disable Gateway API and enable Ingress in your Helm values.
Note: It is recommended to use Gateway API with Envoy Gateway instead of NGINX Ingress Controller (Deprecated).
TLS Certificate Configuration (Required for both options)
Create a Kubernetes secret containing the TLS certificate and private key. This secret is used for TLS termination at the load balancer level.
kubectl create secret tls my-tls-secret --key <private key filename> --cert <certificate filename> -n <namespace>
If you use Gateway API, reference this secret in the TLS listeners of your Gateway manifest.
If you use NGINX Ingress Controller, set tlsSecret to this secret name in Helm values.
Option 1: Envoy Gateway (Gateway API-based approach) - RECOMMENDED
It is recommended to use Gateway API with Envoy Gateway instead of NGINX Ingress Controller. Gateway API provides a more expressive, extensible, and role-oriented API for configuring traffic routing in Kubernetes.
- Install Envoy Gateway.
helm install envoy-gateway oci://docker.io/envoyproxy/gateway-helm \
--version v1.7.0 -n envoy-gateway-system \
--set config.envoyGateway.extensionApis.enableBackend=true \
--set envoyGateway.gateway.experimentalFeatures.enabled=true \
--create-namespace
- Create and apply Gateway and GatewayClass resources.
kubectl apply -f <your-gateway-manifest> -n <namespace>
Ensure that the hostnames and Gateway name in your created Gateway manifest match those configured in your Helm chart values. Additionally the TLS secret created above should be correctly referenced in the listeners of the Gateway resource for TLS termination.
- Create a ConfigMap containing the CA certificate for backend TLS verification and reference it under
backendTLSPolicy.caCertificateConfigMapin the Helm chart values. This is required if you have enabled backend TLS verification in the Gateway configuration.Note: A default ConfigMap with the name
wso2-ca-certis created when thedefaultConfigMapCreationoption is enabled in the values.yaml. This default ConfigMap uses the default certificates provided in the APIM truststore. However, for production deployments, it is recommended to create and manage the ConfigMap with the CA certificate yourself, and setdefaultConfigMapCreationto false
kubectl create configmap wso2-ca-cert --from-file=ca.crt=/path/to/your/certificate.pem -n <namespace>
- Update
values.yamlto enable Gateway API and configure backend TLS policy.
kubernetes:
gatewayAPI:
enabled: true
gatewayName: "wso2-apim-gateway"
defaultConfigMapCreation: false
management:
enabled: true
hostname: "am.wso2.com"
gateway:
enabled: true
hostname: "gw.wso2.com"
websocket:
enabled: true
hostname: "websocket.wso2.com"
websub:
enabled: true
hostname: "websub.wso2.com"
backendTLSPolicy:
enabled: true
caCertificateConfigMap: "wso2-ca-cert"
hostname: "<hostname used in the TLS certificate>"
- If you require further routing customizations, use Gateway API Extensions provided by Envoy.
Option 2: NGINX Ingress Controller (Ingress-based approach) - DEPRECATED
You can install the NGINX Ingress Controller using the official Helm chart
Some sample annotations that can be used with Ingress resources are as follows:
- The ingress class should be
nginxif you are using NGINX Ingress Controller. - The following annotations can be included in Helm values for Ingress resources depending on requirements. Refer to NGINX annotation documentation for details.
ingressClass: "nginx"
ingress:
tlsSecret: ""
ratelimit:
enabled: false
zoneName: ""
burstLimit: ""
controlPlane:
hostname: "am.wso2.com"
annotations:
nginx.ingress.kubernetes.io/backend-protocol: "HTTPS"
nginx.ingress.kubernetes.io/affinity: "cookie"
nginx.ingress.kubernetes.io/session-cookie-name: "route"
nginx.ingress.kubernetes.io/session-cookie-hash: "sha1"
1.2 Mount Keystore and Truststore
- If you are not including the keystore and truststore into the docker image, you can mount them using a Kubernetes secret. Following steps shows how to mount the keystore and truststore using a Kubernetes secret.
- Create a Kubernetes secret with the keystore and truststore files. The secret should contain the primary keystore file, secondary keystore file, internal keystore file, and the truststore file. Note that the secret should be created in the same namespace in which you will be setting up the deployment.
- Make sure to use the same secret name when creating the secret and when configuring the helm chart.
- If you are using a different keystore file name and alias, make sure to update the helm chart configurations accordingly. In addition to the primary, internal keystores and truststore files, you can also include the keystores for HTTPS transport as well.
- Refer the following sample command to create the secret and use it in the APIM.
kubectl create secret generic apim-keystore-secret --from-file=wso2carbon.jks --from-file=client-truststore.jks --from-file=wso2internal.jks -n <namespace>
By default, this deployment uses the default keystores and truststores provided by the relevant WSO2 product. For advanced details with regards to managing custom Java keystores and truststores in a container based WSO2 product deployment please refer to the official WSO2 container guide.
1.3 Configure Internal Encryption Key (Mandatory)
This section is for the internal encryption key (wso2.apim.configurations.encryption.key), which is mandatory and used by API Manager to encrypt and decrypt internal/shared data.
-
Generate a unique 256-bit secret key. If you use OpenSSL, the command will be as follows:
openssl rand -hex 32 -
Add the generated key to the following location in your
values.yaml:wso2: apim: configurations: encryption: key: "<generated-64-char-hex-key>" -
If secrets are encrypted using cipher tool and secure vault according to section 1.4, encrypt the generated internal encryption key and set the encrypted value to
wso2.apim.configurations.encryption.key.
Warning
Distributed and Cloud Deployments
In a distributed or high-availability deployment, all API Manager instances must use the exact same internal encryption key (wso2.apim.configurations.encryption.key). Each instance encrypts and decrypts shared registry resources using this key, so a mismatch will cause decryption failures across the cluster. Configure the shared key on every node before the first startup.
1.4 Encrypting Secrets (Cipher Tool and Secure Vault)
- If you need to use the cipher tool to encrypt the passwords in the secret, first you need to encrypt the passwords using the cipher tool. The cipher tool can be found in the
bindirectory of the product pack. The following command can be used to encrypt the password:sh ciphertool.sh -Dconfigure -Dsymmetric -Dkey.based.encryption - Also, the apictl can be used to encrypt passwords as well. Reference can be found in the documentation.
- Then, the encrypted values should be filled in the relevant fields of
values.yaml. - Since the encryption key is required to resolve the encrypted value at runtime, you need to store the value in the cloud provider's secret manager. You can use the cloud provider's secret store to store the encryption key. The following section can be used to add the cloud provider's credentials to fetch the encryption key. Configuration for AWS can be as below:
aws: secretsManager: secretIdentifiers: secretEncryptionKey: # -- AWS Secrets Manager secret name secretName: "" # -- AWS Secrets Manager secret key secretKey: ""Please note that currently AWS, Azure, and GCP Secrets Managers are only supported for this.
Warning
Use the Same Secret Encryption Key Across All Nodes
If secure vault is enabled, all API-M nodes must use the same secretEncryptionKey reference and underlying key material. A mismatch will cause secret resolution and decryption failures across nodes.
Note
These are two different keys serving distinct purposes. The internal encryption key (wso2.apim.configurations.encryption.key) defined in section 1.3 is mandatory and is used by API Manager for internal encryption of data such as registry resources and shared configuration. The secret encryption key (secretEncryptionKey under AWS/Azure/GCP) is a separate key used only when secure vault is enabled, allowing the runtime to fetch and decrypt secrets stored in a cloud provider's secret manager (which may itself include an encrypted copy of the internal encryption key).
1.5 Configure Docker Image and Databases
-
Add the following configurations to reflect the docker image created previously in the helm chart.
wso2: deployment: image: imagePullSecrets: enabled: false username: "" password: "" registry: "" repository: "" digest: ""If you are using a private Docker registry, you must enable
imagePullSecrets.enabledand provide the username and password. - Provide the database configurations under the following section.- If you need to change hostnames, update them under the Kubernetes Gateway API or Ingress section. - Update the keystore passwords in the security section of thewso2: apim: configurations: databases: apim_db: url: "" username: "" password: "" shared_db: url: "" username: "" password: ""values.yamlfile. - Review the descriptions of other configurations and modify them as needed to meet your requirements. A simple deployment can be achieved using the basic configurations provided in thevalues.yamlfile. All configuration options for each Helm chart are documented in their respective component guides: - All-in-one - Classic Gateway - Update the admin credentials in the configuration directory.# -- Super admin username adminUsername: "" # -- Super admin password adminPassword: ""
1.6 Configure SSL in Service Exposure
SSL Configuration Best Practices
For WSO2 recommended best practices in configuring SSL when exposing internal services to outside of the Kubernetes cluster, refer to the official WSO2 container guide.
Proper SSL configuration is critical for securing API traffic and maintaining compliance with security standards.
2. All-in-One Configurations¶
This section covers the specific configurations relevant to the All-in-One deployment pattern.
2.1 Configure Multiple Gateways
If you need to distribute the Gateway load that comes in, you can configure multiple API Gateway environments in WSO2 API Manager to publish to a single Developer Portal. See more...
gateway:
# -- APIM Gateway environments
environments:
- name: "Default"
type: "hybrid"
gatewayType: "Regular"
provider: "wso2"
visibility:
displayInApiConsole: true
description: "This is a hybrid gateway that handles both production and sandbox token traffic."
showAsTokenEndpointUrl: true
serviceName: "apim-gw-wso2am-gateway-service"
servicePort: 9443
wsHostname: "websocket.wso2.com"
httpHostname: "gw.wso2.com"
websubHostname: "websub.wso2.com"
- name: "Default_apk"
type: "hybrid"
provider: "wso2"
gatewayType: "APK"
displayInApiConsole: true
description: "This is a hybrid gateway that handles both production and sandbox token traffic."
showAsTokenEndpointUrl: true
serviceName: "apim-gw-wso2am-gateway-service"
servicePort: 9443
wsHostname: "websocket.wso2.com"
httpHostname: "default.gw.wso2.com:9095"
websubHostname: "websub.wso2.com"
2.2 Configure User Store Properties
You can configure user store properties as described in this documentation:
userStore:
# -- User store type.
type: "database_unique_id"
# -- User store properties
properties:
ReadGroups: true
Configuration Note
If you do not want to configure any of these properties, you must remove the properties block from the YAML file to prevent deployment issues.
For a complete list of available user store properties and their descriptions, refer to the documentation.
2.4 Configure JWKS URL
By default, for the super tenant, the Resident Key Manager's JWKS URL is set to https://<HOSTNAME>:9443/oauth2/jwks. If you are using a virtual host like am.wso2.com that is not globally routable, this URL will be incorrect. You can configure the correct JWKS URL for the super tenant using the Helm chart as shown below:
wso2:
apim:
configurations:
oauth_config:
oauth2JWKSUrl: "https://localhost:9443/oauth2/jwks"
2.5 Deploy All-in-One
After configuring all the necessary parameters, you can deploy the All-in-One pattern using Helm:
- Create a namespace for your deployment
- Install the Helm chart with your custom configurations
# Create namespace for deployment
kubectl create namespace <namespace>
# Deploy API Manager using Helm
helm install <release-name> <helm-chart-path> \
--version 4.7.0-1 \
--namespace <namespace> \
--dependency-update \
-f values.yaml \
--create-namespace
Deployment Parameters
<release-name>: Choose a name for your release (e.g.,apim)<namespace>: Specify the Kubernetes namespace (e.g.,wso2)<helm-chart-path>: Path to the Helm chart (e.g.,./all-in-oneor use the repository URL)
3. Add a DNS record mapping the hostnames and the external IP¶
Obtain the external IP (ADDRESS) of Gateway API resources by listing Gateway objects.
kubectl get gateway -n <NAMESPACE>
If you are using Ingress instead of Gateway API, obtain the external IP from Ingress resources.
kubectl get ing -n <NAMESPACE>
Use the value from ADDRESS or EXTERNAL-IP as the external IP.
If the defined hostnames (in the previous step) are backed by a DNS service, add a DNS record mapping the hostnames and the external IP in the relevant DNS service.
If the defined hostnames are not backed by a DNS service, for the purpose of evaluation you may add an entry mapping the
hostnames and the external IP in the /etc/hosts file at the client-side.
<EXTERNAL-IP> <kubernetes.gatewayAPI.management.hostname> <kubernetes.gatewayAPI.gateway.hostname> <kubernetes.gatewayAPI.websub.hostname> <kubernetes.gatewayAPI.websocket.hostname>
4. Access Management Consoles¶
-
API Manager Publisher:
https://<kubernetes.gatewayAPI.management.hostname>/publisher -
API Manager DevPortal:
https://<kubernetes.gatewayAPI.management.hostname>/devportal -
API Manager Carbon Console:
https://<kubernetes.gatewayAPI.management.hostname>/carbon -
Classic Gateway:
https://<kubernetes.gatewayAPI.gateway.hostname>